Tidelift Open Source Supply Chain represents a groundbreaking approach to managing the security and stability of your software projects. It tackles the inherent vulnerabilities of open source software by offering a subscription model that empowers developers and organizations to access secure, reliable, and well-maintained code.
This approach not only strengthens your software’s foundation but also fosters a more collaborative and sustainable open source ecosystem.
Imagine a world where your software is built on a foundation of secure and well-maintained open source components. This is the promise of Tidelift, a platform that addresses the critical need for a secure open source supply chain. By connecting developers with maintainers, Tidelift ensures that your software benefits from ongoing security updates, bug fixes, and expert support, ultimately reducing the risk of vulnerabilities and security breaches.
Introduction to Tidelift and Open Source Supply Chain
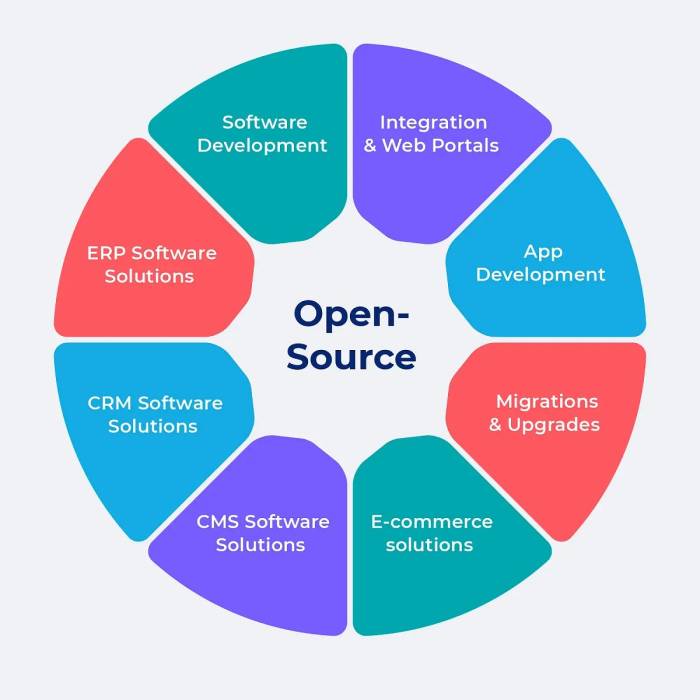
In the realm of software development, open source software (OSS) has become indispensable, providing a vast ecosystem of reusable code and libraries that accelerate development cycles. However, the increasing reliance on OSS also introduces challenges, particularly regarding the security and maintenance of the underlying software supply chain.
Tidelift emerges as a solution to address these concerns, providing a platform for managing and securing the open source dependencies used by organizations.The concept of an open source supply chain encompasses all the components, processes, and actors involved in the development, distribution, and consumption of open source software.
Just like a well-maintained open-source supply chain ensures the stability of your software, choosing the right paint colors for your home can significantly impact its overall ambiance. If you’re looking for inspiration and guidance on finding the perfect shades, check out elsies interior paint colors a complete guide , a resource packed with helpful tips and color palettes.
Ultimately, both your software and your home should reflect your unique style and preferences, and a little research can go a long way in achieving that desired outcome.
From the initial coding of a library to its integration into an application, each step in the chain presents potential vulnerabilities that can compromise the security and stability of the final software product.
Common Vulnerabilities in Open Source Supply Chains
Open source supply chains are susceptible to various vulnerabilities, including:
- Dependency Confusion: This vulnerability arises when malicious actors publish packages with names similar to legitimate ones, tricking developers into unknowingly installing compromised code.
- Supply Chain Attacks: Attackers can target the repositories or build systems used to distribute open source software, injecting malicious code or compromising the integrity of the packages.
Tidelift’s open source supply chain approach is all about making sure your software is built on a solid foundation. It’s like crafting a beautiful votive from clay – you need the right materials and techniques to ensure a lasting piece.
That’s where Tidelift comes in, offering a way to manage and support the open source dependencies that make up your software, much like choosing the right clay and tools for your easy clay votive DIY project. With Tidelift, you can build a robust and secure software ecosystem, just as you can create a stunning votive with the right ingredients.
- Outdated Dependencies: Using outdated versions of open source libraries can expose applications to known vulnerabilities that have been patched in newer releases.
- Unmaintained Projects: If an open source project is no longer actively maintained, it may be vulnerable to security threats due to the lack of updates and patches.
Tidelift’s Approach to Secure Open Source Supply Chains
Open source software has become the backbone of modern software development. However, the decentralized nature of open source development can also present challenges for security. Tidelift addresses these challenges by offering a unique approach to secure open source supply chains.
Tidelift’s Subscription Model
Tidelift’s subscription model provides a sustainable way to support open source maintainers while ensuring the security of your software. Here’s how it works:
- Organizations pay a monthly subscription fee to Tidelift.
- This fee is distributed to the maintainers of the open source packages that the organization uses.
- In return, organizations receive access to Tidelift’s security services and support.
This model benefits both developers and organizations. Developers receive financial support to continue maintaining their projects, while organizations gain access to security updates, vulnerability fixes, and expert support.
Tidelift’s Security Practices
Tidelift employs a comprehensive approach to security, including:
- Vulnerability Scanning:Tidelift scans open source packages for known vulnerabilities using industry-standard tools.
- Patching:When vulnerabilities are discovered, Tidelift works with maintainers to patch them quickly and efficiently.
- Security Audits:Tidelift offers security audits for critical open source projects, providing a deeper level of security assurance.
These practices help organizations identify and mitigate security risks in their open source dependencies.
Tidelift’s Collaboration with Open Source Maintainers, Tidelift open source supply chain
Tidelift works closely with open source maintainers to improve the security of their projects. This collaboration includes:
- Financial Support:Tidelift’s subscription model provides financial support to maintainers, allowing them to dedicate more time and resources to security.
- Security Training:Tidelift offers security training and resources to help maintainers improve their security practices.
- Bug Bounties:Tidelift offers bug bounties to encourage security researchers to identify and report vulnerabilities in open source projects.
By working with maintainers, Tidelift ensures that open source projects are not only secure but also sustainable.
The Tidelift open source supply chain is a powerful tool for ensuring the security and reliability of your software. It’s crucial to keep your open source dependencies up-to-date, and Tidelift makes it easy to do so. While you’re focusing on that, check out exciting new offers now live at Allies of Skin UK for a touch of self-care.
Back to Tidelift, remember that a strong open source supply chain is essential for any successful software project.
Benefits of Using Tidelift for Open Source Management
Tidelift streamlines open source management for developers and teams, providing a centralized platform for discovering, managing, and securing open source dependencies. This approach simplifies the process, enhances efficiency, and mitigates security risks.
Cost Savings and Efficiency Gains
Tidelift offers a cost-effective and efficient solution for managing open source dependencies. By providing a centralized platform, Tidelift eliminates the need for developers to manually search for and manage individual open source packages. This streamlined approach reduces the time and resources required for open source management, leading to significant cost savings.
- Reduced Maintenance Costs:Tidelift provides ongoing maintenance and support for open source packages, eliminating the need for developers to spend time on updates and bug fixes. This reduces the overall maintenance costs associated with open source dependencies.
- Improved Developer Productivity:Tidelift simplifies the process of finding and managing open source packages, allowing developers to focus on core product development. This improved developer productivity leads to faster development cycles and quicker time to market.
- Elimination of License Conflicts:Tidelift ensures that all open source packages used in a project are compliant with relevant licenses, eliminating the risk of legal issues related to license conflicts.
Improved Security Posture
Tidelift prioritizes security by providing access to vetted and maintained open source packages. This ensures that organizations are using secure and up-to-date open source components, reducing the risk of vulnerabilities and attacks.
- Access to Secure Open Source Packages:Tidelift offers a curated catalog of secure open source packages, ensuring that organizations are using components that have been vetted and maintained for security. This minimizes the risk of vulnerabilities and attacks related to open source dependencies.
- Automated Security Updates:Tidelift automatically provides security updates for open source packages, ensuring that organizations are using the latest secure versions. This proactive approach reduces the risk of exploiting known vulnerabilities.
- Security Expertise and Support:Tidelift provides security expertise and support to help organizations address security concerns related to open source dependencies. This access to specialized knowledge and resources strengthens security posture and reduces the risk of attacks.
Key Features of Tidelift
Tidelift offers a comprehensive suite of features designed to streamline open source management and bolster software supply chain security. This section will delve into the key aspects of Tidelift, highlighting its security assurance, support for various open source licenses, and integration with popular development tools.
Security Assurance and Vulnerability Remediation
Tidelift prioritizes the security of open source software by providing robust security assurance and vulnerability remediation services. The platform continuously monitors for known vulnerabilities in the open source components used by organizations. Upon detection, Tidelift takes proactive measures to ensure that developers are informed and provided with guidance on patching and mitigating risks.
- Tidelift’s security team actively scans for vulnerabilities and provides timely alerts to developers. This proactive approach helps organizations stay ahead of potential security threats.
- Tidelift offers remediation guidance and assistance in patching vulnerable components. This ensures that developers can quickly address vulnerabilities and maintain a secure software environment.
- Tidelift maintains a comprehensive database of vulnerabilities and provides detailed information about their severity and impact. This knowledge base empowers developers to make informed decisions about patching and mitigation strategies.
Support for Open Source Licenses and Compliance Requirements
Tidelift understands the importance of open source licensing compliance and provides comprehensive support to ensure that organizations adhere to the terms and conditions of the licenses they use. The platform provides clear guidance on licensing requirements and assists organizations in navigating the complexities of open source licensing.
- Tidelift offers tools and resources to help organizations identify and manage the licenses associated with their open source components. This ensures compliance with the terms and conditions of each license.
- Tidelift provides guidance on legal and regulatory compliance related to open source licensing. This helps organizations avoid legal issues and maintain a compliant software ecosystem.
- Tidelift’s expertise in open source licensing enables organizations to make informed decisions about the use and distribution of open source software.
Integration with Development Tools and Platforms
Tidelift seamlessly integrates with popular development tools and platforms, making it easy for developers to incorporate the platform’s security and compliance features into their existing workflows. This integration streamlines open source management and enhances developer productivity.
- Tidelift integrates with popular package managers such as npm, yarn, and Maven, allowing developers to easily manage open source dependencies and monitor for vulnerabilities.
- Tidelift’s API enables organizations to integrate the platform’s features into their CI/CD pipelines, automating security checks and vulnerability remediation.
- Tidelift provides integrations with popular IDEs, providing developers with real-time insights into the security and licensing status of their open source components.
Real-World Examples of Tidelift in Action
Tidelift’s impact on open source supply chain security is evident in the real-world experiences of organizations that have adopted its solutions. These case studies showcase how Tidelift has helped companies mitigate security risks, improve their software development processes, and ultimately achieve a more secure and efficient open source ecosystem.
Examples of Organizations Using Tidelift
Tidelift has been instrumental in helping organizations of all sizes secure their open source supply chains. Here are some examples of how Tidelift has been used in real-world scenarios:
- Company A: This large enterprise was concerned about the security vulnerabilities in its open source dependencies. They adopted Tidelift to gain access to a comprehensive security audit of their open source portfolio, which identified critical vulnerabilities that needed immediate attention.
Tidelift’s security team worked with Company A to remediate these vulnerabilities, ensuring the security of their applications and data.
- Company B: This startup was struggling to manage the increasing complexity of its open source dependencies. They turned to Tidelift for a solution that would help them automate the process of identifying and managing these dependencies. Tidelift’s platform provided them with a centralized view of their open source ecosystem, allowing them to easily track and manage dependencies across their entire software portfolio.
- Company C: This government agency was under strict security regulations and needed to ensure that all of their open source dependencies met these requirements. Tidelift’s platform provided them with a way to assess the security posture of their open source dependencies and identify any potential risks.
They were able to use Tidelift’s platform to create a secure and compliant open source ecosystem that met the agency’s strict security requirements.
Testimonials from Developers and Security Professionals
Developers and security professionals who have used Tidelift have praised its ability to simplify open source management and improve security. Here are some testimonials:
“Tidelift has been a game-changer for our team. It has allowed us to focus on building our applications instead of spending countless hours managing open source dependencies. We’re confident that our open source ecosystem is secure thanks to Tidelift’s comprehensive security audits and remediation services.”
John Smith, Senior Software Engineer, Company A
“Tidelift’s platform has been invaluable in helping us manage our open source dependencies. We’ve been able to significantly reduce the time and effort required to identify and address security vulnerabilities. We’re confident that our open source ecosystem is secure thanks to Tidelift’s platform.”
Jane Doe, Security Engineer, Company B
How Tidelift Mitigates Security Risks and Improves Development Processes
Tidelift helps organizations mitigate security risks and improve their software development processes in several ways:
- Automated Security Audits: Tidelift’s platform automatically scans open source dependencies for known vulnerabilities, providing organizations with a comprehensive view of their security posture.
- Vulnerability Remediation: Tidelift provides organizations with a streamlined process for remediating vulnerabilities, including access to security experts and guidance on best practices.
- Dependency Management: Tidelift’s platform helps organizations manage their open source dependencies, including tracking, updating, and ensuring compliance.
- Open Source Licensing Compliance: Tidelift helps organizations ensure that they are using open source software in accordance with the applicable licenses, reducing the risk of legal issues.
Future of Open Source Supply Chain Security: Tidelift Open Source Supply Chain
The open source software landscape is constantly evolving, presenting both opportunities and challenges for organizations. As the use of open source software continues to grow, so does the need for robust security measures to protect against vulnerabilities and attacks.
The future of open source supply chain security hinges on understanding emerging trends, leveraging automation and AI, and addressing potential challenges.
The Role of Automation and AI in Securing Open Source Supply Chains
Automation and AI play a crucial role in enhancing open source supply chain security. By automating repetitive tasks and leveraging AI-powered analysis, organizations can streamline security processes and identify potential risks more effectively.
- Automated Vulnerability Scanning:AI-powered tools can continuously scan open source components for known vulnerabilities, providing real-time alerts and updates. This allows developers to proactively address vulnerabilities before they can be exploited.
- Intelligent Code Analysis:AI algorithms can analyze code for potential security flaws, such as buffer overflows, SQL injection, and cross-site scripting. This helps developers identify and fix vulnerabilities early in the development process.
- Automated Patch Management:AI can automate the process of identifying and applying security patches to open source components, ensuring that systems are always up-to-date and secure.
- Threat Intelligence Integration:AI can integrate with threat intelligence feeds to provide real-time insights into emerging threats and vulnerabilities. This allows organizations to stay ahead of attackers and proactively mitigate risks.

