The Unfolding Financial Ruin: Decoding the True Cost of a Data Breach
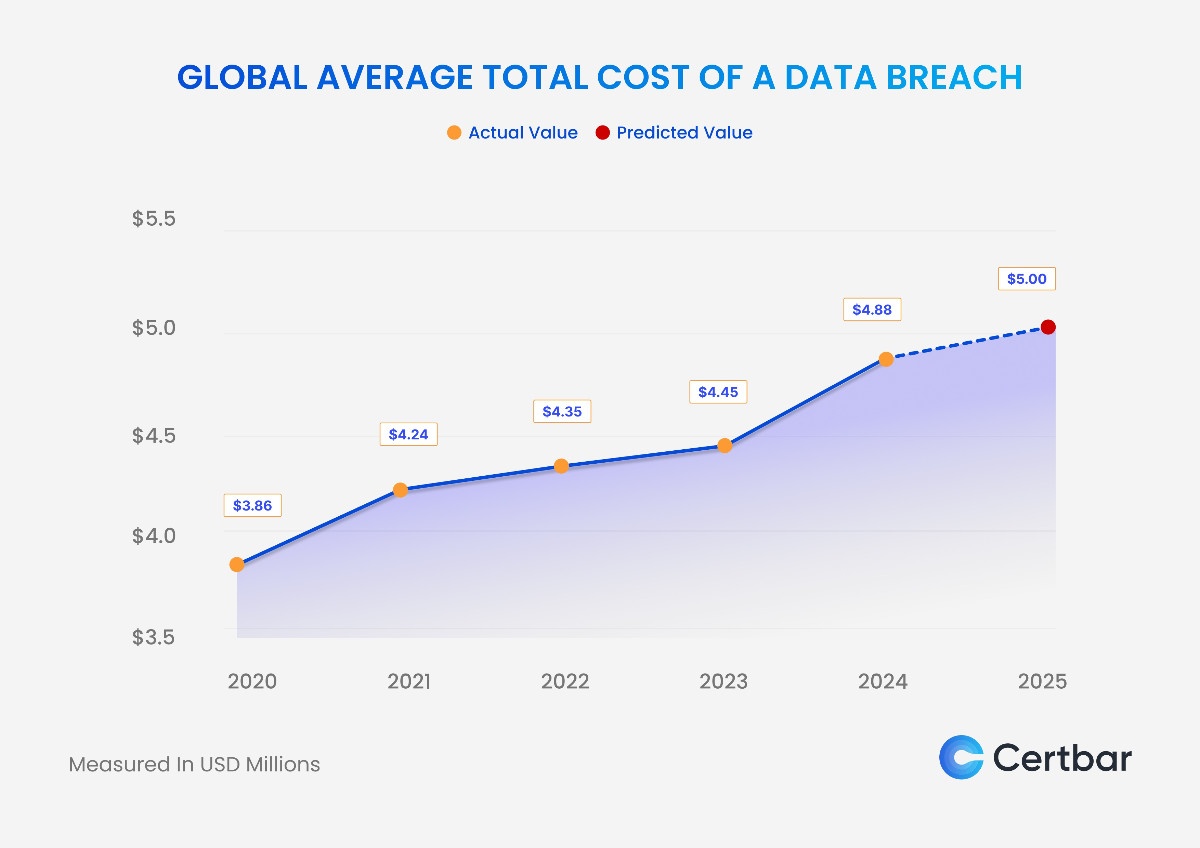
The economic repercussions of a data breach extend far beyond immediate remediation. Quantifying the precise cost is a complex undertaking, influenced by a multifaceted array of direct and indirect expenses. At its core, a data breach represents a catastrophic failure in cybersecurity, exposing sensitive information – personal, financial, or proprietary – to unauthorized access and potential misuse. This exposure triggers a cascade of financial obligations, often leaving organizations reeling from the fallout for years. The average total cost of a data breach, a metric diligently tracked by cybersecurity research firms, consistently demonstrates a significant upward trend, underscoring the escalating threat landscape and the increasing sophistication of cyber adversaries. These figures, often in the millions of dollars, serve as a stark reminder of the financial vulnerabilities inherent in digital operations.
Direct costs represent the most tangible and immediately observable financial impact of a data breach. These encompass the expenses directly associated with identifying, containing, and recovering from the incident. Forensic investigation services are a primary component, involving specialized cybersecurity firms to determine the root cause, scope, and nature of the breach. Their expertise is crucial for understanding how attackers gained access, what data was compromised, and the extent of the damage. These investigations are often conducted under intense pressure and can be exceedingly expensive due to the specialized skills and tools required. Following the investigation, the cost of incident response teams, comprised of internal and external cybersecurity professionals, becomes a significant expenditure. These teams work around the clock to neutralize the threat, eradicate malicious actors from the network, and restore compromised systems.
Data recovery and system restoration are further critical direct costs. Depending on the severity of the breach and the extent of data loss or corruption, organizations may need to invest heavily in restoring lost data from backups or, in worst-case scenarios, rebuilding entire systems. This can involve substantial hardware and software expenses, as well as the cost of labor for implementing and testing these new or restored infrastructures. Legal counsel is another substantial direct expense. Data breaches almost invariably lead to legal ramifications, including regulatory investigations, potential litigation from affected individuals, and class-action lawsuits. Engaging experienced cybersecurity lawyers is imperative to navigate the complex legal landscape, manage regulatory compliance, and defend against legal challenges. Notification costs, mandated by various data privacy regulations, also contribute significantly. This involves informing all affected individuals about the breach, detailing the nature of the compromised data and the steps they should take to protect themselves. This often requires significant investment in communication platforms, mailing services, and dedicated call centers to handle inquiries from concerned customers, employees, or partners.
Beyond the immediate financial outflows, indirect costs, though often harder to quantify, can have a more profound and long-lasting impact on an organization’s financial health. The most significant indirect cost is the damage to reputation and brand erosion. News of a data breach spreads rapidly, severely impacting customer trust and loyalty. Consumers are increasingly wary of entrusting their personal information to companies that have demonstrated a failure in protecting it. This loss of trust can translate into declining sales, reduced market share, and difficulty attracting new customers. The long-term consequences of reputational damage can be devastating, requiring years of concerted effort and significant investment in public relations and customer engagement initiatives to rebuild confidence.
Business interruption and lost productivity represent another substantial indirect cost. During and immediately after a breach, systems may be taken offline for investigation and remediation, halting operations and leading to significant downtime. This cessation of business activities directly translates into lost revenue and missed opportunities. Furthermore, employees may be distracted by the incident, spending valuable work hours dealing with the fallout rather than focusing on their core responsibilities. This reduction in productivity, while difficult to measure precisely, contributes to the overall economic burden of the breach.
Regulatory fines and penalties are a growing component of the indirect cost of data breaches. Governments worldwide are enacting and enforcing stricter data privacy regulations, such as the GDPR in Europe and the CCPA in California, which impose substantial penalties for non-compliance and data protection failures. These fines can range from a percentage of an organization’s global annual turnover to fixed sums, depending on the severity of the violation and the jurisdiction. The threat of these penalties incentivizes organizations to invest more heavily in cybersecurity measures to avoid such punitive financial repercussions. Increased insurance premiums are another indirect cost. Following a data breach, cybersecurity insurance providers will likely reassess the risk profile of the affected organization, leading to significantly higher premiums for future coverage. In some cases, obtaining insurance may become more challenging or even impossible, leaving the organization more exposed to future incidents.
The cost of remediation and ongoing security enhancements is also a critical factor. A data breach often exposes inherent weaknesses in an organization’s existing cybersecurity infrastructure. To prevent future incidents, significant investments are required to upgrade security systems, implement new technologies, and conduct comprehensive security audits. This includes the cost of new hardware, software licenses, and the training of IT staff to manage and operate these advanced security solutions. The ongoing nature of cybersecurity threats necessitates continuous adaptation and improvement, making these investments a recurring operational expense.
Furthermore, the cost of lost intellectual property and trade secrets, while often the most difficult to assign a monetary value, can be the most devastating. For many organizations, proprietary information, such as product designs, research data, customer lists, and strategic plans, represents their most valuable assets. The theft or exposure of this information can provide competitors with a significant advantage, leading to market disruption and the erosion of competitive edge. The long-term financial implications of losing intellectual property can be far-reaching, impacting future product development, market positioning, and overall profitability.
The industry in which an organization operates significantly influences the cost of a data breach. Highly regulated industries, such as healthcare and finance, typically incur higher costs due to stricter compliance requirements and the sensitive nature of the data they handle. For instance, a breach in a healthcare organization not only exposes patient health information (PHI) but also carries the risk of HIPAA violations, leading to substantial fines and reputational damage. Financial institutions, dealing with sensitive financial data and credit card information, face similar regulatory scrutiny and a heightened risk of widespread fraud. Conversely, breaches in less regulated sectors might still be costly but may not carry the same level of regulatory penalties.
The size of the organization also plays a role. Larger enterprises often have more extensive datasets and a larger customer base, meaning a breach can affect a greater number of individuals and involve a wider array of sensitive information, thereby increasing the overall cost. However, smaller businesses can be disproportionately affected. Lacking the robust security infrastructure and financial reserves of larger corporations, a significant data breach can be an existential threat, leading to bankruptcy. Their limited resources make it harder to absorb the immediate remediation costs, legal fees, and the long-term damage to their reputation.
The type of data compromised is a critical determinant of the cost. Breaches involving personally identifiable information (PII), such as social security numbers, driver’s license numbers, and financial account details, are particularly costly due to the potential for identity theft and financial fraud. Health records (PHI) and payment card data (PCI) also command high remediation and regulatory penalty costs. When intellectual property or trade secrets are stolen, the long-term economic damage can be incalculable, as it impacts competitive advantage and future revenue streams.
The response to the breach itself significantly influences the ultimate cost. A swift, transparent, and well-executed incident response plan can mitigate the damage. Conversely, a slow, disorganized, or secretive response can exacerbate the situation, leading to greater regulatory scrutiny, increased legal liability, and more severe reputational harm. The proactive implementation of robust cybersecurity measures, including regular risk assessments, employee training, and the deployment of advanced security technologies, can not only prevent breaches but also reduce the cost and impact should an incident occur. Investing in proactive security is a far more cost-effective strategy than reacting to a breach after it has happened. The ongoing evolution of cyber threats demands a continuous cycle of assessment, adaptation, and investment in cybersecurity. Organizations must view cybersecurity not as a cost center, but as a strategic imperative for business continuity and long-term financial stability. The true cost of a data breach is a dynamic and escalating figure, demanding constant vigilance and a commitment to robust security practices.