
JupiterOne Funding Attack Surface: Fortifying Digital Assets in a Dynamic Funding Landscape
The burgeoning world of venture capital and private equity, while fueling innovation, concurrently expands an organization’s attack surface, particularly for companies leveraging platforms like JupiterOne for security and asset management. Understanding and mitigating the funding-related attack surface is no longer a niche concern but a critical imperative for safeguarding sensitive data, intellectual property, and operational integrity. This article delves into the multifaceted attack surface created by funding activities, the specific vulnerabilities exploited, and how JupiterOne, when optimally configured and utilized, can serve as a pivotal tool in a robust defense strategy.
Funding rounds, whether seed, Series A, or later-stage, invariably introduce new entities, systems, and data flows into an organization’s ecosystem. Investors, auditors, legal counsel, and due diligence teams require access to a wide array of information, ranging from financial records and intellectual property portfolios to customer data and operational metrics. Each of these interactions, if not meticulously secured, presents a potential entry point for malicious actors. The increased pace and volume of communication, document sharing, and system access associated with funding initiatives create a temporary but heightened risk profile. This is where a comprehensive understanding of the "funding attack surface" becomes paramount.
The attack surface can be broadly categorized into several interconnected areas, each amplified by funding activities. Firstly, data exposure risk is significantly elevated. During due diligence, vast amounts of sensitive data are shared. This includes, but is not limited to, proprietary algorithms, trade secrets, customer lists, personally identifiable information (PII), financial projections, and internal operational documentation. Inadequate access controls, insecure file-sharing methods, or compromised endpoints used by external parties can lead to data breaches. The sheer volume of data exchanged increases the probability of misconfigurations or oversights that expose critical information.
Secondly, third-party risk is amplified. Investors and their representatives often necessitate integration with their own systems or require temporary access to the startup’s environments. This introduces new software, APIs, and potentially less secure infrastructures into the trusted network. Compromised third-party tools or employee accounts within these entities can serve as a pivot point into the funded company’s assets. The onboarding and offboarding of these temporary access points, if not managed with rigorous security protocols, leave lingering vulnerabilities.
Thirdly, credential compromise becomes a more attractive target. With increased external access and the need for rapid information dissemination, individuals involved in the funding process may be more susceptible to phishing attacks or social engineering attempts. Attackers can impersonate investors, lawyers, or financial advisors to solicit login credentials or sensitive information, thereby gaining unauthorized access to internal systems and data repositories. The urgency and pressure associated with closing funding rounds can lower vigilance.
Fourthly, insider threats, while always present, can be exacerbated by the emotional and financial stakes involved in funding. Disgruntled employees, or those with financial motivations, might exploit the heightened access granted during funding to exfiltrate data or disrupt operations. The increased scrutiny on financial performance can also create an environment where individuals feel pressured to manipulate data or provide privileged access to external parties for personal gain.
Fifthly, supply chain vulnerabilities are a critical concern. Many startups rely on a complex web of vendors and service providers. During funding, these dependencies become more visible and potentially more vulnerable. If a critical service provider used by the startup experiences a breach, and that breach exposes data related to the funding process, the startup’s reputation and security posture can be severely damaged. JupiterOne’s ability to map these dependencies becomes crucial here.
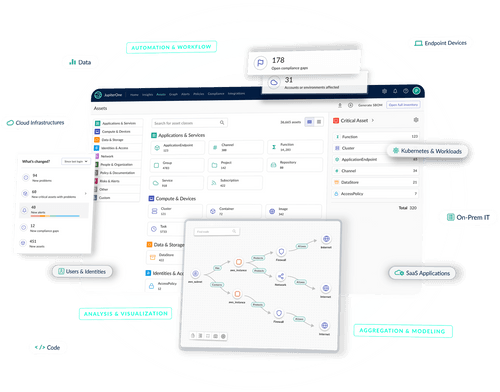
JupiterOne’s foundational strength lies in its ability to provide a centralized, continuously updated inventory of an organization’s digital assets. During funding, this capability becomes indispensable for mapping and securing the expanded attack surface. By ingesting data from various sources – cloud environments, SaaS applications, code repositories, identity providers, and security tools – JupiterOne creates a comprehensive graph of an organization’s digital footprint.
For the data exposure risk, JupiterOne can meticulously inventory all data repositories, classify sensitive data, and identify who has access to it. During funding, this means understanding precisely which documents, databases, or cloud storage buckets contain sensitive information that will be shared. JupiterOne can then enforce policies to ensure that access to this data is restricted to authorized individuals and that sharing mechanisms are secure, for instance, by identifying instances of sensitive data residing in publicly accessible cloud storage buckets or unencrypted databases. Its ability to track data lineage can also help in understanding where data has flowed during the due diligence process, aiding in post-deal audits.
Regarding third-party risk, JupiterOne excels at mapping out the interconnectedness of an organization’s technology stack. During funding, it can identify all third-party applications and services that will be involved in the due diligence process or will require access to the startup’s systems. By visualizing these connections, security teams can proactively assess the security posture of these third parties, identify potential vulnerabilities introduced by their integration, and ensure that access is provisioned with the principle of least privilege. This includes identifying shadow IT or unsanctioned tools that might be used to facilitate data sharing.
The mitigation of credential compromise is intrinsically linked to JupiterOne’s identity and access management (IAM) capabilities. By integrating with identity providers, JupiterOne can provide visibility into user accounts, their privileges, and their activity. During funding, this allows for tighter control over temporary accounts, role-based access controls (RBAC), and the enforcement of multi-factor authentication (MFA) for all external parties and internal stakeholders involved in the process. JupiterOne can flag accounts with excessive privileges or those that have not been used recently, prompting review and potential revocation of access. Its continuous monitoring can also detect anomalous login patterns indicative of credential compromise.
For insider threats, JupiterOne’s asset inventory and activity monitoring can provide crucial insights. By understanding the legitimate access patterns of employees and contractors, anomalies can be more readily detected. For example, if an employee suddenly begins accessing or exfiltrating unusually large amounts of data that are not related to their job function, JupiterOne can flag this activity. This proactive detection can enable swift intervention before a significant breach occurs. Furthermore, by enforcing policies around data access and segregation, JupiterOne can limit the scope of potential insider damage.
Addressing supply chain vulnerabilities is a core strength of JupiterOne’s asset graph. By mapping all interconnected systems and services, JupiterOne can identify the critical dependencies that might be exposed during funding. If a third-party vendor involved in the due diligence process is found to have known vulnerabilities, JupiterOne can immediately highlight the potential impact on the organization and trigger remediation efforts. This visibility allows for a more informed risk assessment of the entire technology supply chain, ensuring that no critical links are overlooked when securing the funding process.
Beyond these specific categories, JupiterOne’s policy-as-code capabilities are invaluable for standardizing and automating security controls related to funding. Security policies can be defined to automatically check for compliance with access control requirements, data encryption standards, and vulnerability management for any new assets or integrations introduced during funding rounds. This ensures consistency and reduces the risk of human error.
Furthermore, JupiterOne’s reporting and auditing features are essential for demonstrating compliance and for post-event analysis. During funding, investors and regulators often require proof of robust security practices. JupiterOne can generate comprehensive reports on asset inventory, access controls, vulnerability assessments, and incident history, providing auditable evidence of the organization’s security posture. In the unfortunate event of a breach, these reports can be instrumental in forensic investigations and in understanding the root cause.
The key to effectively leveraging JupiterOne against the funding attack surface lies in proactive engagement. Security teams must work in lockstep with finance, legal, and business development teams throughout the entire funding lifecycle. This includes:
-
Pre-funding Security Assessment: Before engaging with potential investors, conduct a thorough assessment of the current security posture using JupiterOne. Identify and remediate any existing vulnerabilities that could be exposed during due diligence. This includes hardening cloud environments, reviewing access controls, and ensuring data encryption is in place.
-
Investor Onboarding Security Protocols: Establish clear security protocols for onboarding investors and their representatives. This should include defined access request and approval processes, mandatory security awareness training for all involved parties, and the use of secure, encrypted communication and file-sharing channels. JupiterOne can help in defining and enforcing these protocols.
-
Data Minimization and Access Control: During due diligence, adhere to the principle of data minimization. Only share the absolute minimum amount of sensitive data required. Implement granular access controls within JupiterOne to ensure that individuals only have access to the specific data and systems they need. Revoke access promptly after it’s no longer required.
-
Continuous Monitoring and Alerting: Configure JupiterOne for continuous monitoring of all relevant assets and user activity. Set up alerts for suspicious activities, unauthorized access attempts, or deviations from security policies. This allows for rapid detection and response to potential threats.
-
Post-Funding Security Review: Once funding is secured, conduct a comprehensive security review. Ensure that all temporary access granted during the process has been revoked. Analyze the data flows and integrations that were established and assess any residual risks. JupiterOne’s inventory can be used to ensure a clean slate and to incorporate any new mandated security requirements from investors.
In conclusion, the funding process, while vital for growth, undeniably introduces a dynamic and often complex attack surface. Organizations must recognize that the increased interactions, data sharing, and third-party involvement create a fertile ground for cyber threats. JupiterOne, with its comprehensive asset inventory, continuous monitoring, policy enforcement, and granular visibility, provides an indispensable platform for understanding, managing, and fortifying this funding-related attack surface. By proactively integrating JupiterOne into their funding strategies and adhering to rigorous security protocols, organizations can significantly mitigate risks, protect their valuable digital assets, and ensure a more secure path to growth. The effective utilization of JupiterOne transforms a potential period of heightened vulnerability into an opportunity to demonstrate and enhance an organization’s commitment to security, thereby building trust with investors and safeguarding long-term success.